.png)
Learn how U.S. courts authenticate audio and video evidence using FRE 901/902, chain of custody, hash checks, and forensic analysis. Video and audio recordings now decide everything from police misconduct cases to corporate fraud investigations.
Video and audio recordings now decide everything from police misconduct cases to corporate fraud investigations.
But before a jury sees a single frame, the court asks a much simpler question:
Can this recording be trusted?
That is why audio-video evidence authentication is now a core litigation issue in 2026. A weak foundation can lead to exclusion. Even when the media is admitted, poor handling records can reduce credibility and invite aggressive cross-examination.

This guide explains how U.S. courts evaluate authenticity, which Federal Rules of Evidence matter most, how examiners test alleged manipulation, and what operational controls make sensitive media defensible. The practical takeaway is simple, courts do not require perfection, but they do require a reliable, documented process.
In federal court, authenticity is about proving that evidence is what the offering party says it is. Under Rule 901(a), the proponent must present enough support for a reasonable factfinder to conclude the item is genuine.
Two points are often misunderstood:
You do not have to disprove every hypothetical tampering theory at the admissibility stage.
Courts may admit a recording and still let the jury decide how much trust to place in it.
That distinction is increasingly important as deepfake allegations become more common in litigation. Courts generally expect specific evidence of alteration, not generic claims that “anything can be faked.”

Courts are increasingly seeing arguments that video or audio evidence could be synthetic.
However, judges have generally rejected generic deepfake arguments unless supported by technical analysis.
Typical judicial expectations include:
• forensic examination
• metadata analysis
• compression artifact review
• expert testimony under Rule 702
Without concrete evidence of manipulation, courts usually treat deepfake claims as arguments affecting weight, not admissibility.
Rule 901 provides multiple paths for authenticating media. In practice, courts usually rely on a combination of:
No single checklist controls every case. Judges look at the totality of the foundation.
Rules 902(13) and 902(14) can allow certain electronic evidence to be authenticated by certification rather than live testimony, especially where integrity is shown through digital identification methods such as matching hash values.
In practical terms, if your process captures media in a forensically sound way and preserves stable hashes across lifecycle events, you reduce avoidable admissibility fights.
The “best evidence” framework matters when parties offer clips, exports, or transcodes:
Authenticity disputes become harder when only derivative clips are produced without a clear explanation of what happened to the original.
When manipulation is alleged, experts often become central. Under Rule 702, the court evaluates whether methods are reliable, based on sufficient facts, and reliably applied. Daubert and related cases reinforce the judge’s gatekeeping role.
Most audio & video evidence authentication disputes are won or lost on records, not rhetoric.
Chain of custody does not require a zero-risk environment. It requires a documented, explainable, and reproducible history of how evidence moved and changed (if at all).
At a minimum, defensible workflows usually include:
A defensible workflow often looks like this:
If this chain is complete, custodians and experts can confidently explain reliability. If it is incomplete, opposing counsel has clear grounds for attack.
Legal foundation and forensic testing should reinforce each other. Strong examiners use multiple methods rather than relying on any single “tamper indicator.”
Examiners analyze container metadata, codec fields, device markers, file-system timestamps, and conversion history. They compare these findings to witness timelines and known system behavior.
Metadata alone is rarely conclusive, but contradictions often trigger deeper scrutiny.
Frame and sequence analysis can identify discontinuities, inconsistent motion patterns, abrupt GOP structure changes, or suspicious transition boundaries.
The key is context: not every discontinuity means tampering. Some anomalies are expected in normal export or platform transcode workflows.
Experts evaluate compression artifacts and quantization behavior to distinguish ordinary delivery pipeline changes from suspicious localized recompression.
This step helps avoid false positives in modern multi-platform media handling.
For audio, examiners assess waveform continuity, background noise profile, spectral consistency, and A/V synchronization behavior.
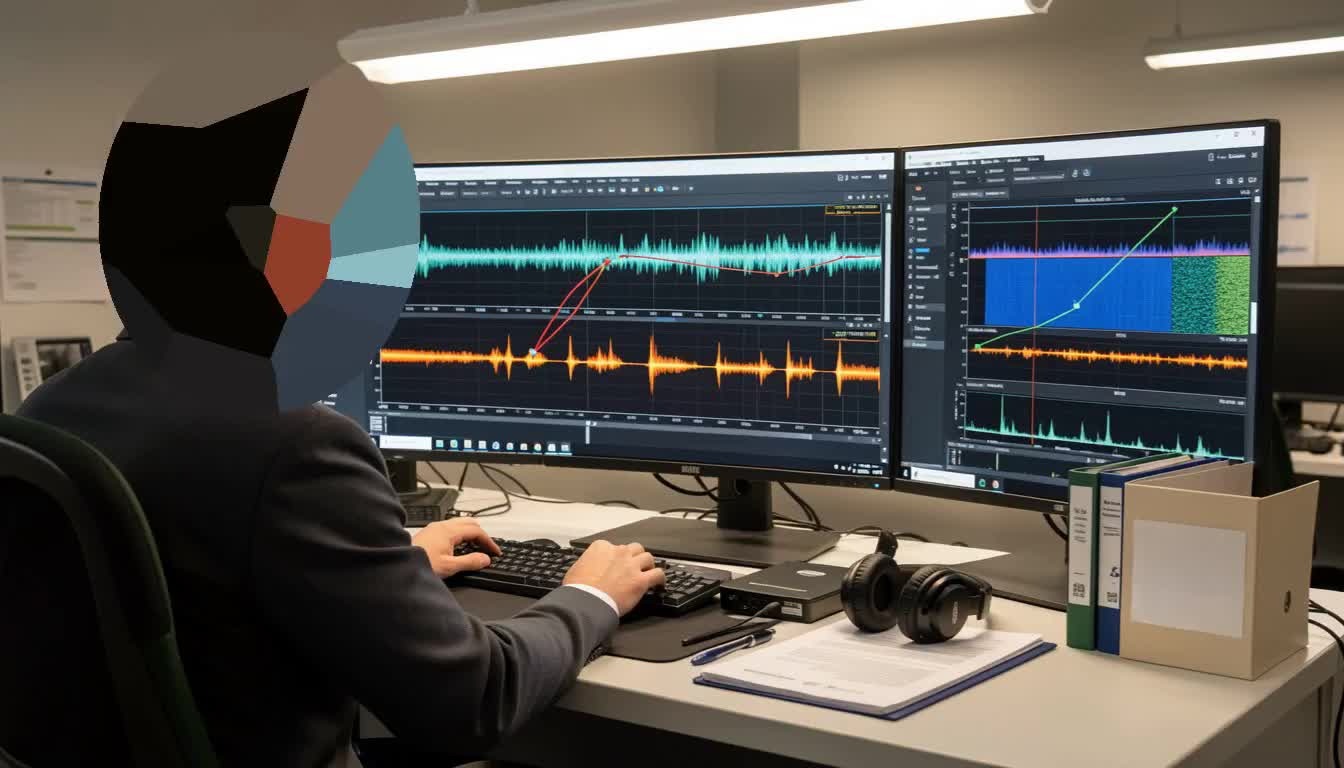
Inserted or rearranged segments can leave detectable spectral or temporal inconsistencies, even when edits sound natural to human listeners.
Redaction is often legally required. But redaction can also create authenticity challenges when parties cannot reconstruct what was changed, by whom, and why.
The standard is not full public visibility of sensitive content. The standard is process transparency.
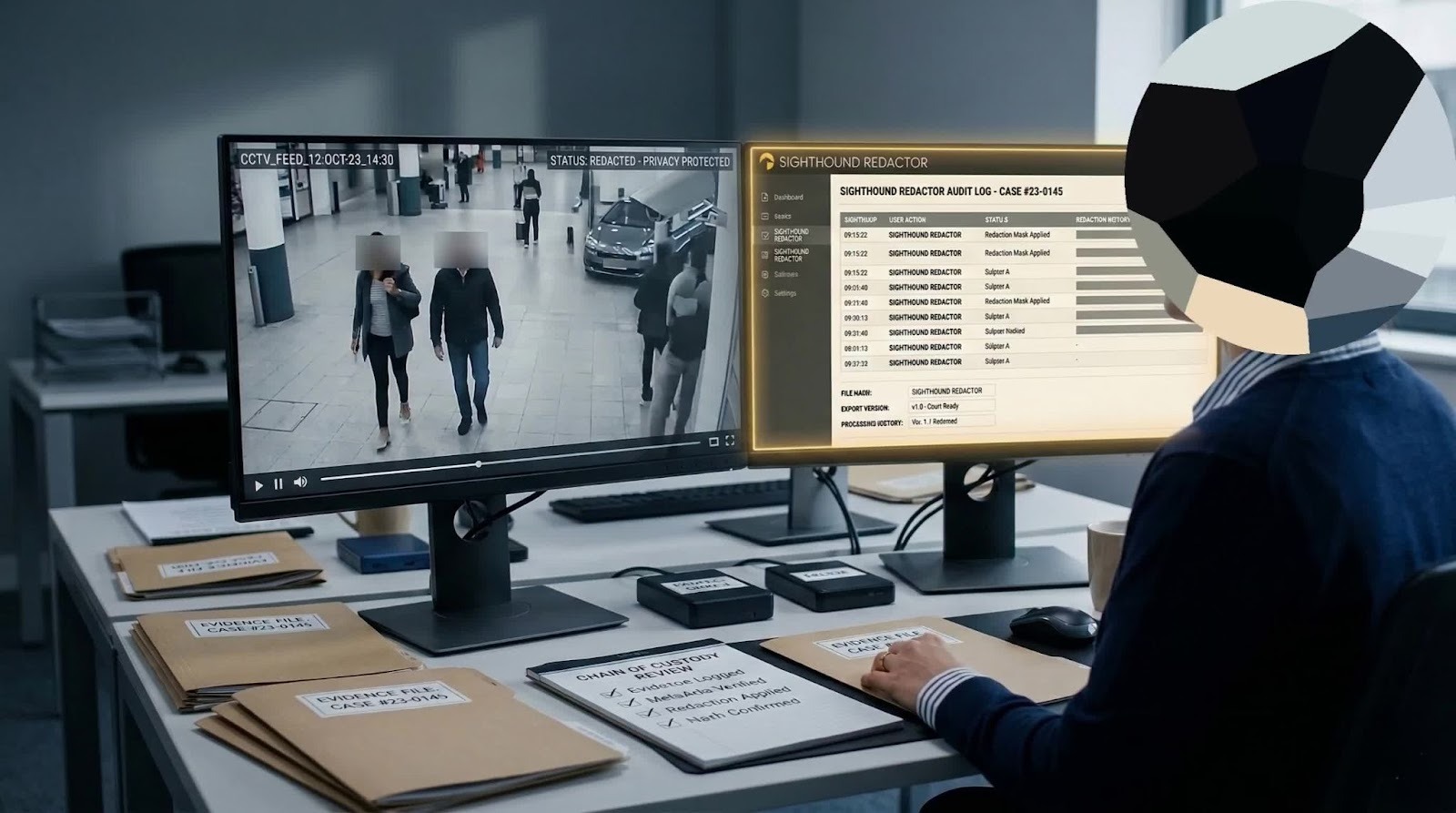
High-value documentation usually includes:
This is where tools like Sighthound Redactor can fit naturally in legal workflows. Used correctly, it helps teams preserve originals, process derivative copies, and maintain structured audit artifacts. The legal value is not the brand name itself; it is the repeatable, reviewable workflow.
If your redaction process cannot be independently explained six months later, it is not court-ready.
Typical challenge: Allegation of deletion, insertion, or synthetic manipulation.
Typical response: Combine witness foundation, forensic findings, and custody logs to show provenance and process consistency.
Typical challenge: Missing or unclear custody events.
Typical response: Close transfer gaps with documented chain records, access logs, and custodian testimony.
Typical challenge: Excerpt attacks under best-evidence principles.
Typical response: Preserve source media and document how excerpts were generated, including time ranges and transformation history.
Typical challenge: Rule 702/Daubert attack on method reliability.
Typical response: Use validated methods, clear limitations analysis, and testable, reproducible findings.
Organizations that consistently succeed in audio-video evidence authentication usually operationalize a simple discipline:

Teams using Sighthound Redactor often map these controls into standard operating procedures so legal, compliance, and technical teams follow the same evidence-handling model.
The strongest audio-video evidence authentication outcomes come from operational discipline long before a hearing. Courts evaluate legal foundation, technical reliability, and documentation quality together.
If you preserve originals, verify integrity with hashes, keep complete chain-of-custody records, and document each redaction/export event, you significantly improve admissibility and credibility.
For legal and compliance teams, the strategic shift is straightforward: treat evidentiary integrity as a system design requirement, not a last-minute litigation exercise.
If your organization handles sensitive video evidence, maintaining defensible redaction and audit trails is essential.
You can see how Sighthound Redactor supports evidence review and compliant redaction workflows here: www.redactor.com
Need a live demo? Schedule a Redactor demo now.
Published on: